Posts by :
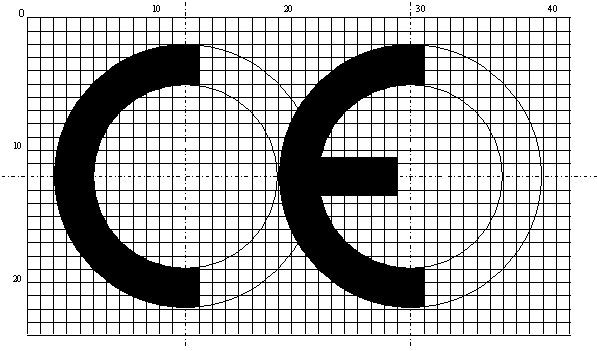
CE MARKING, EMC and LVD REQUIREMENTS
The most widely used marking on products today is undoubtedly the CE logo. This sign of conformity with European Union norms in fact symbolizes the conformity of the product used with the relevant technical standards of the European Union. In terms of electrical and electronic devices, this marking means that the product is designed and manufactured according to the;
- relevant EU standards
- Electromagnetic Compatibility (EMC) Directive
- Low Voltage Directive (LVD)
The relevant EU standards are standards, which are specific to the product family, including functional tests that are sometimes required. However, more than the functional tests, the important issue for CE are the EMC and LVD standards, directed by the product family standard.
So, What about the directives?
Directives are the regulations announced by European Parliament and Council about a spesific topic, which contain the basic principles on that subject and all member states have to apply for the subject matter. As I mentioned above, there are two directives for CE in terms of electrical and electronic products, EMC and LVD. We have to remember the main principle that directives does not directly point out the tests to be applied, standards to be used or technical information etc…It sets the principles on the subject, explains the method of implementation, determines the responsibilities and describes the actions and penalties in case of non-compliance.
I have shared basic information about EMC in my previous articles. The European Union’s directive on general principles of EMC for CE marking is 2014/30 /EU at the time of writing this article (you can reach the original directive by clicking the link). It, in general, introduces the fundamental procedures for ensuring EMC requirements (the product is electromagnetically able to operate without disturbing its surroundings more than allowed and also not disturbed from the electromagnetic effects surrounding it). Therefore, it must be ensured that the relevant product conforms to EMC standards.
The other essential requirement, as in EMC, is the compliance with the Low Voltage Directive (LVD). LVD is aiming to take measures to protect the health and safety of people, animals and goods in the market. The current EU directive is 2014/35/EU. We can say that the directive basically aims at enforcing related products safety standards.
Both directives share basic principles as I mentioned above. As a summary the most basic titles you will see in the content will be;
- Requirements for placing the product on the market
- Obligations of the manufacturer, representative, importers, distributors
- Conformity assessment procedures, declarations
- Non-compliance and penalties
There are two important points to be considered in CE marking;
First, preparation and storage of a Technical File containing reports showing the conformity of the product with the above directives, technical information about the product, explanatory documents etc. The other is to make the correct markings and to issue the necessary information on the product, its packaging or in the documents sent with the product. These details are set out in the contents or Annexes of the relevant directives. The most important issue, of course, is to take into account the latest version, the last one containing all the updates.
Do You Know That The Information In Your PC Is Spreading Around??
We know that electrical and electronic equipment may have intentionally or unintentionally electromagnetic energy radiation to their surroundings. Wireless transmitters, mobile phones, radars, detectors, wireless data transmission systems do voluntarily emit this energy. But it is not desirable for a computer, copier or projection device to emit electromagnetic energy around. As I mentioned in my previous article, TEMPEST is a term that refers to unintentional electromagnetic energy emissions caused from electrical and electronic equipment that process confidential information, and also a code name by U.S. to investigate, examine, and control such emissions.
Although it seems utopian, TEMPEST is quite an old method of intelligence. Once energy emitted from the electrical device is picked up by an antenna and receiver, it can be amplified and reprocessed, and sometimes image refined thus information leakage can be obtained. This method was brought to Turkey by a team that I myself was a member of, in 1990’s, a laboratory and technical infrastructure that can create, solve and test the TEMPEST Problem with completely national abilities was established and personnel were trained. The most striking point of the problem is that leakage from any information processing device can be obtained … information displayed on the computer screen, information read on the CD drive, information replicated on the copier, transmitted by fax, scanned on the scanner, printed on the printer … all the information processing equipment that can come into your mind, is a potential TEMPEST leak source.
Are you sure that your PC is safe with the precautions you had taken???
The simplest TEMPEST scenario is that; while you are writing a CONFIDENTIAL article in your computer, the exploiter is collecting the signals electromagnetically spreading from your screen and reconstructing it… just like collecting aerial broadcast information sent over kilometers and watching a TV programme in our living room… This process can be done surreptitiously upstairs, in the next building or in a panelvan with darkened glass parking in front of your office…just like you do not know who is watching your television broadcasts! This kind of leak is known as “radiated emissions leakage”. Another way of collecting information leaks beyond using an antenna is to penetrate the network which the information processing device is connected and reach to the information … Going through the same example, CONFIDENTIAL information in your computer can also be obtained by penetrating to the power network or internet network it is connected to, collecting the data by a monitoring probe, even from hundreds of meters away..! This method is known as “conducted emissions leakage”. Neither the update of the antivirus on your system, nor the power of your firewall means anything against TEMPEST, because if the information is open on your screen, the same information exists in the air and on your network, and therefore on the exploiters antenna and probe…
So, how can we become safe against TEMPEST Leaks??
Actually the risk is big, but some measures are quite easy. First, I must say that the only and safest measure of the leakage through the conducted emissions is the TEMPEST filtering to be done on the signal lines or the power lines. Filters are devices that prevent leaks out without affecting the operation of the device. Leaks caused by radiated emissions can be prevented by the use of special designed equipment. During my years at TÜBİTAK – UEKAE, I have directed National TEMPEST Filters, National TEMPEST Proof IT Equipment development projects. Today, thousands of devices we have developed are used in many critical govermental institutions and military areas. If you do not have a chance to use these special devices of high cost, you should pay attention to work in the special chambers with TEMPEST proof or having a large controlled zone by taking advantage of the principle that leakage signals decrease inversely with distance.
This article was published in periodical “Science and Technology to Everybody (Herkese Bilim Teknoloji)”, March 10th, 2017.
What Would We Do Without Technology ?
Technology, though, if our preference or not, we have already put into every aspect of our lives. So, even when considering these issues I need to look at images from the Internet, and write using my tablet..At Paris Charles de Gaulle airport, free wireless internet available everywhere, enslaved thousands of people in the waiting saloons, heads all bend forward, having been broken from the world, just indulged to smartphones or tablets. The 3-4 year-old babies watching cartoons on the tablets, using it as skillfull as a baby bottle,at the sam time retired ladies and gentlemen over 70 years old, no matter which country they are from, are in social networking shares..a very familiar picture, a common picture we may face wherever we go nowadays.
We live in an age that we feel naked and vulnerable, with constant restlessness when our mobile phone is not with us. Naturally, we often ask the question “what were we doing in the past ??”..We are likely to have forgotten how we communicated without technology. Yesterday I very clearly saw the answer in Cuba. In this respected country where internet and smartphones are not popular even in the largest city, Havana, people had not distorted the overall face to face communication. A rubber ball or a wooden toy is enough for the presence of childrens intimate sharings, where the olders keep the small traders affections and street chats of the neighbors in front of the doors of the houses even a nail is not driven for 40 years. Although we have forgotten, life was exactly like that for those X generation and older, like me. So how is the picture in Havana? Music everywhere, entertainment at every corner, and most importantly, a lot of smiles, lots of hearty laughter and happy conversations.
The picture for sure destroys the idea of necessity of technology to be happy, furthermore, leads to think as if technology is just an instrument to miss the good old days. But we still say “at least we should not give up internet..!” helplessly. “We can not be happy without technology” is no longer so easy for me to say ..
Electromagnetic Information Leaks: TEMPEST
The facilities we provide for living in the age of information technology are making information being processed with technological improvements more and more common every day. We are now able to carry information in discs about the size of a finger where not so much, back to 20 years ago, the same information was only be reached through hundreds of books on the shelves. All the libraries in the world are as close as our smartphone in our pocket …
A common feature of information-processing technologies is being under usage of electrical and electronic systems. This is, for sure, also the open door firstly applied by unauthorized persons who wish to access information. We know that electrical and electronic equipment voluntarily or unintentionally radiate some electromagnetic energy to their surroundings. The effect of this energy on the performance of the devices is observed under Electromagnetic Compatibility (EMC) subject. In terms of information security, there is a very serious threat in this case. TEMPEST is a code name that describes the work carried out to collect, examine, and reconstruct the information contained in electromagnetic energy emitted from electrical and electronic equipment. Although it seems like an abbreviation, TEMPEST is a name given by U.S. to the works in this subject. Yes, it may seem quite utopian at first sight, but TEMPEST has been used since the 1950s. The information is reconstructed by processing the electromagnetic leaks that propagate from the body of the information processing device to the air or to power network to which it is connected through its conductors. If this information is classified (confidential) information, of course the value is very high.
The first use of TEMPEST for intelligence purposes is that the British MI5 organization in the 1960s obtained information from France’s cryptographic communication in this way. However, during the Second World War, America had worked on this method and obtained a variety of information with similar principles, it can be understood from the documents that lost confidentiality today.
The first scientific and completely open work on TEMPEST was in 1985, an experiment and the paper explaining it by Wim Van Eck, a Dutch telecom researcher. The experiment showed that a computer’s screen can be reconstructed from the electromagnetic emissions, meters away from the source.
So, what is the situation in Turkey ???
TEMPEST technology was brought to our country in the 1990s by a team that I was also a memeber of. In TÜBİTAK National Cryptology Institute, a TEMPEST laboratory was established and put in service for Turkish Armed Force and govermental bodies, by a protocol signed with the General Staff. So, although a little bit late compared to some leading states, the technology can still be pursued with national possibilities. The question that needs to be emphasized here is, what technologies do these advanced nations develop in our country’s today?
This article was published in periodical “Science and Technology to Everybody (Herkese Bilim Teknoloji)”, February 10, 2017.